Multi-Factor Authentication
For many corporations, multi-factor authentication is now a must. The advances made in computing technologies now make it possible to break most of the every-day passwords with relative ease. In order to prevent this, it has become imperative to add a second layer of security to protect network resources.
Authentication Factor
An authentication factor is a type of credential used for identity verification purposes. There are three main authentication factors:
-
Knowledge Factor – Implies something a user knows (password)
-
Possession Factor – Implies something a user has (hardware / software token)
-
Inheritance Factor – Implies something a user is (fingerprint, DNA, retina / iris, voice)
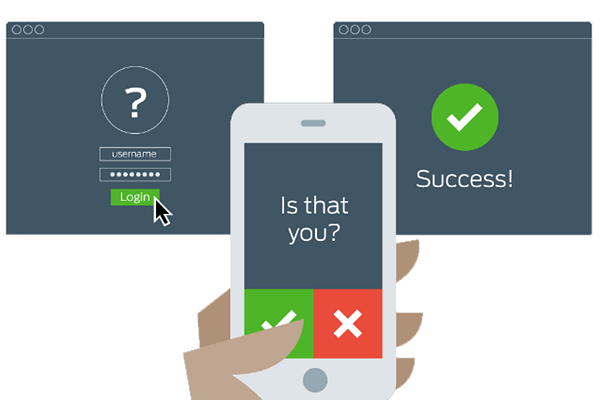
Although it is possible to integrate inheritance factor to multi-factor authentication schemes, generally knowledge and possession factors are used for multi-factor authentication purposes due to cost and ease of use. Multi-factor authentication allows a corporation to tie a specific token (software or hardware) to a user and prevent logins of users that do not have an authenticator. With Multi-factor authentication, even if a password of a user was leaked out or cracked, the perpetrator would not be able to login to the network without the users’ authenticator.
An authenticator can be a hardware device, or a software that is installed on a smartphone. Hardware authenticators also can be either offline (no connection) type devices where a specific algorithm creates a series of symbols where a user need to types it manually, and online devices where these devices can be configured to connect to the computer and automatically allow the login of the user once connected and send the corresponding signal.
Multi-factor authentication implementation can be done to secure access to virtually all authentication systems that support RADIUS authentication, such as Virtual Private Network (VPN), Outlook Web Access (OWA), Remote Desktop Protocol (RDP) and more.